Featured
Table of Contents
Vpn Protocols Compared: Which Is The Best?
Still, it is worth pointing out that SSTP is natively built into Windows platforms, so it's simpler to establish than Open, VPN. In general, both Open, VPN and SSTP are a good choice, but Open, VPN is merely more effective. In case you 'd like to discover more about SSTP, take a look at this post.
Desire to find out more about Wireguard? Then have a look at this post. It's safe to state that both Open, VPN and Soft, Ether are truly safe and secure protocols. They're open-source, utilize military-grade ciphers like AES, make use of 256-bit encryption, and likewise utilize SSL 3. 0. The main distinction in between them is the age Soft, Ether is much more recent than Open, VPN.
In terms of speed, Soft, Ether fares much better than Open, VPN. In fact, according to the research study from the University of Tsukuba (the people behind Soft, Ether VPN, so not a 100% subjective source), the Soft, Ether protocol is expected to be 13 times faster than the Open, VPN protocol.
Openvpn - Wikipedia
You need to know that even if you use a VPN service provider who offers Soft, Ether connection, you'll still require to download additional software for it to run. With Open, VPN, that's optional. Like Open, VPN, Soft, Ether can likewise run its own server, however the Soft, Ether server can actually run the Open, VPN protocol, along with other procedures like IPSec, L2TP/IPSec, SSTP, and Soft, Ether.
In the end, Soft, Ether is a strong Open, VPN alternative. If for whatever factor you can't use Open, VPN, you ought to try Soft, Ether. If you wish to understand more about it, follow this link. For beginners, PPTP is considerably weaker than Open, VPN in regards to security. While Open, VPN can deal with 256-bit file encryption keys and ciphers like AES, PPTP can just use 128-bit keys through the MPPE cipher.
Though, you need to be more cautious with IPSec when configuring it, because a small error can destroy the protection it provides. Also, because IPSec occupies kernel space (the space on the device booked for the operating system), its security can be restricted by the way it's configured by the vendor.
What Is Openvpn?
Still, you need to understand that IPSec might take longer to negotiate the tunnel than Open, VPN does. Interested in learning more about IPSec? Take a look at this post. Open, VPN and IKEv2 are both safe protocols, but it's worth noting that Open, VPN uses TLS/SSL to protect information at the Transportation level, while IKEv2 protects data at the IP level.
And while IKEv2 was established by Cisco together with Microsoft, that's not such a big problem because there are open-source executions of IKEv2. Open, VPN provides more support when it concerns cross-platform compatibility, but IKEv2 is normally a favorite of mobile users because it's natively incorporated into Black, Berry devices.
What does that suggest? That if, for instance, you were to switch from a Wi, Fi connection to your data prepare connection on the go, IKEv2 might manage that without dropping the connection. Besides that, you should know that IKEv2 tends to be faster than Open, VPN, however it's likewise simpler to obstruct than the Open, VPN procedure.
Vpn Protocols And Connection Types - Ipvanish
Our tunneling procedure.
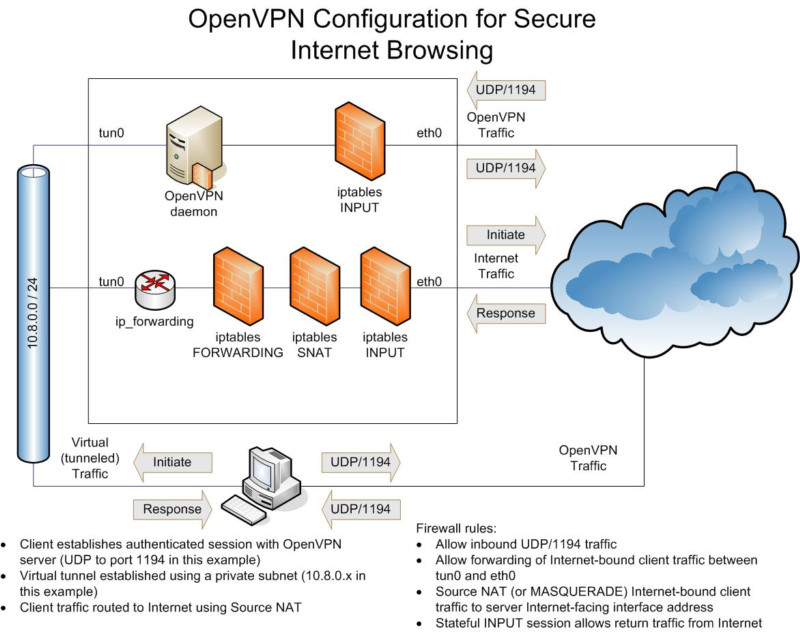
The Open, VPN Community Edition (CE) is an open source Virtual Private Network (VPN) task. It produces safe and secure connections online utilizing a customized security procedure that uses SSL/TLS. This community-supported OSS (Open Source Software application) project, utilizing a GPL license, is supported by numerous Open, VPN Inc. designers and factors in addition to the prolonged Open, VPN community.

Open, VPN is an open source connection procedure used to help with a protected tunnel in between 2 points in a network. In layman's terms, this suggests that it is a relied on technology used by numerous virtual private networks, or VPNs, to ensure any information sent out over the internet is encrypted and personal.
What Is A Vpn & How Does It Work?
It's not unusual to visit a VPN site and see them boasting about the fact that they use Open, VPN as a feature.
No single tool or encrypted connection to the web can ensure your security and privacy, and Open, VPN is no different. There are great reasons why it is thought about one of the most safe connections, which we'll cover below.
A few of the links in this post are affiliate links, which implies that at no additional cost to you, I may be compensated if you select to utilize some of the services listed. I only recommend what I personally use and I hope that the free details supplies value to you! Before we dive deeper into responding to the concern "what is Open, VPN" and how it works, let's take an action back to make certain we're clear on what a VPN protocol is.
What Is A Vpn? How Does It Work And Why Do You Need ...
If you leave your home to go out to consume, there are certain things you will think about: the security of the path, the best mode of transportation, what you need to take with you, and so on. Similarly, when data travels through a channel, it follows specific guidelines. And there isn't just one set of guidelines to follow.
Maybe you have actually become aware of these protocols prior to. They generally pass an acronym such as: Point-to-point tunneling procedure Layer 2 tunneling protocol Web key exchange variation 2 Safe and secure socket tunneling protocol, What is Open, VPN when compared to each of the protocols listed above? There's actually one huge difference: It is open source.
Latest Posts
Best Vpns For Remote Workers & Freelancers In 2023
Best Vpn Solution For Your Business
The Best Vpn For Business In 2023: Top 8 Corporate ...